Many external client applications still use OAuth 1.0a (HMAC-SHA 1 signature method) and they can be integrated with MuleSoft Anypoint Platform. As a useful protocol, OAuth 1.0a is not obsolete or irrelevant. As of version 1.0a (RFC 5849 is 1.0a), there are no known vulnerabilities that make it less secure than 2.0, and in fact it is arguably more secure by default. OAuth 1.0a is just as capable of handling most use cases.
The primary change from version 1 to 2 was the removal of the complicated signature system. This signature system was designed to ensure only the client can use the user tokens, since it relies on a shared secret. However, every request must be individually signed. Version 2 instead relies on SSL/TLS to handle message authenticity. This means that OAuth 2.0 requires HTTPS. We need to be able to provide authentication for all sites, not just those with HTTPS. While the OAuth RFC requires SSL for some endpoints, OAuth 1.0a does not. This is a willful violation of the RFC, as we need to support non-SSL sites.
OAuth 1.0a is used for server to server communication based applications.
What you'll learn
- What are the short comings of using static OAuth 1.0a components' values in mule flow?
- How to use DataWeave to dynamically compute Oauth 1.0a parameters?
- How to integrate OAuth 1.0a application effortlessly using MuleSoft Anypoint Studio (Mule 4) using an example Twitter developer application?
What you'll need
- Anypoint Studio 7.x - https://www.mulesoft.com/lp/dl/studio
- Twitter Developer Portal Account
Authenticating with OAuth 1.0a
OAuth authentication is done in three steps:
- The consumer obtains an unauthorized request token.
- The user authorizes the request token.
- The consumer exchanges the request token for an access token.
Parameters of consumer request:
- oauth_consumer_key = A value used by the consumer to identify itself to the service provider.
- oauth_token = A request token value used by the Consumer to obtain authorization from the User, and exchanged for an Access Token.
- oauth_signature_method = The signature method the Consumer used to sign the request.
- oauth_timestamp = The timestamp is expressed in the number of seconds unless otherwise specified by the service provider. Must be a positive integer value equal or greater than the value used in previous requests.
- oauth_nonce = A nonce is a random string, uniquely generated for each request. The nonce allows the Service Provider to verify that a request has never been made before and helps prevent replay attacks when requests are made over a non-secure channel (such as HTTP).
- oauth_version = Value MUST be 1.0
- oauth_signature = The signature encodes the consumer secret and token secret into a verifiable value which is included with the request. The service provider verifies the signature as specified in each method. When verifying a consumer signature, the service provider should check the request nonce to ensure it has not been used in a previous consumer request.
Parameters of service provider grants:
- oauth_token = The access token value obtained from the developer application.
- oauth_token_secret = The access token secret value obtained from the developer application.
OAUTH 1.0a authentication flow
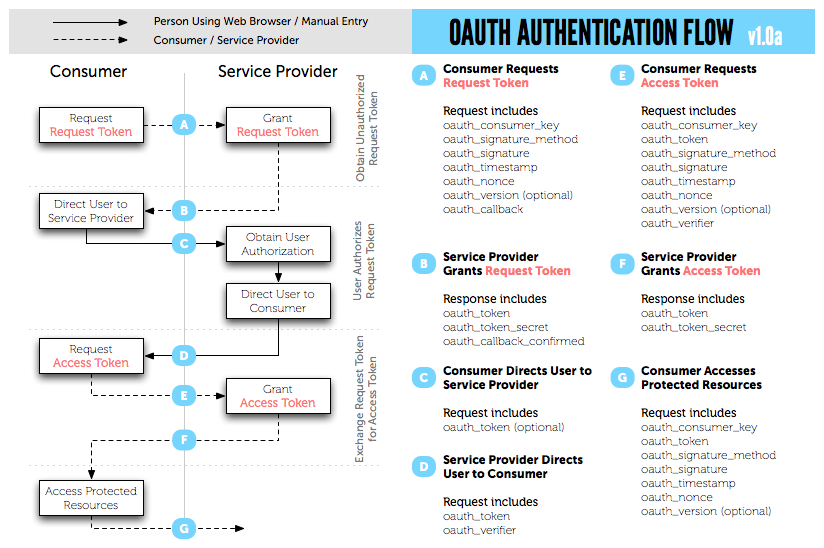
Source: Oauth 1.0a
- Create a Twitter Developer Portal account and create a project app.
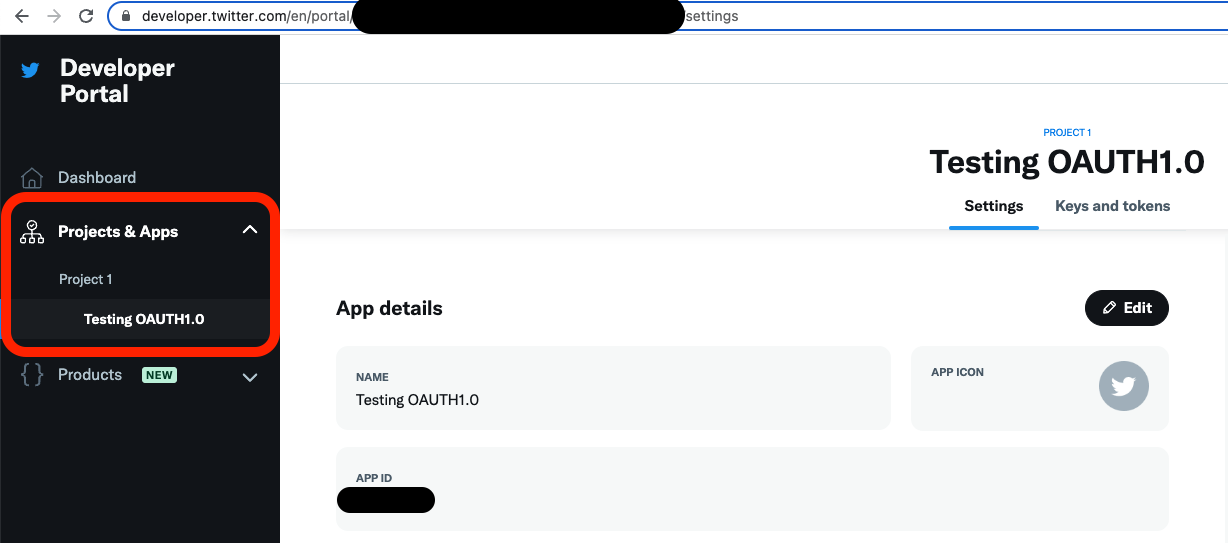
- Click on "Keys and tokens" tab.
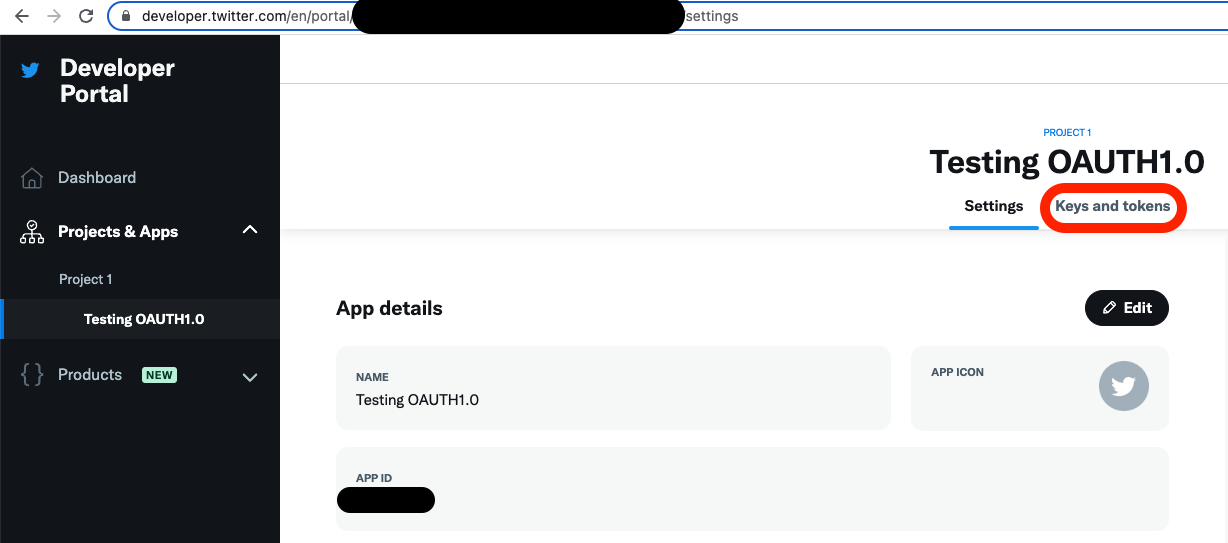
- Click on "Generate" for to get values for API Key and Secret under "Consumer Keys".
- Click on "Generate" for to get values for Access Token and Secret under "Authentication Tokens".
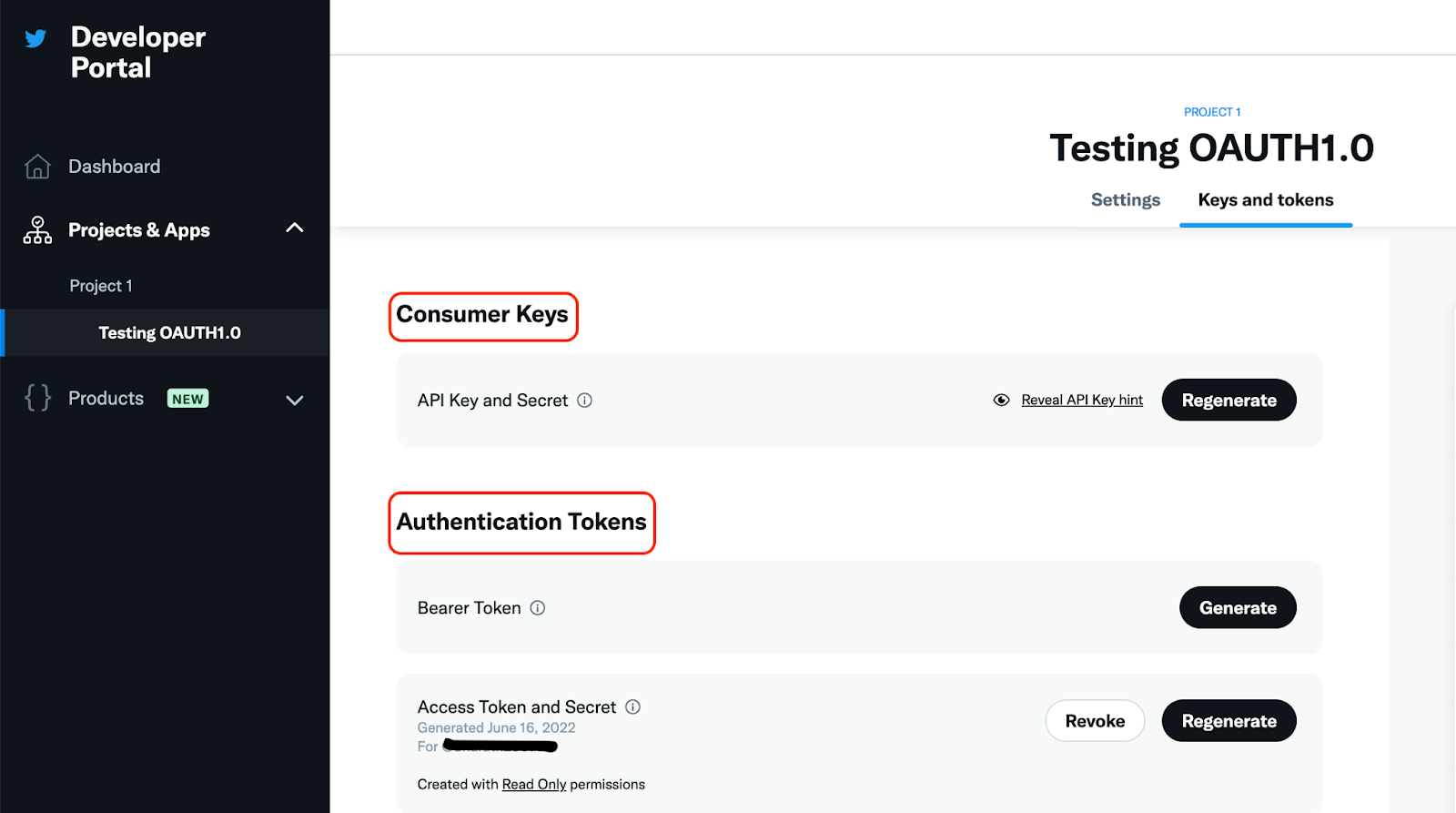
- Copy down the values which will be used in Mule application.
- Create a Mule project and create a configuration file with following value.
YAML file containing the values:
twitter: host: "api.twitter.com"
- Create a HTTP Listener Connector Configuration with default values and define a path for "Listener" component.
- Drag "Set Variable" component and define the value to take in query parameters value →
message.attributes.queryParams.id - Create a HTTP Request Connector Configuration with default values and define "Host" value →
${twitter.host}taken from YAML file. - Drag "Request" component and define values with "Path" value set to
/1.1/statuses/lookup.jsonand "Body" value set topayload - Headers tab - Click on "Add Variable" with user defined values. For Example:
"Name" = "Authorization"and"Value" = Oauth 1.0a signature components as shown below.
'OAuth oauth_consumer_key="4xxxxxxxxxxxxxxxxxxx",oauth_token="1xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx",oauth_signature_method="HMAC-SHA1",oauth_timestamp="1xxxxxxxxx",oauth_nonce="kxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx",oauth_version="1.0",oauth_signature="kxxxxxxxxxxxxxxxxxxxxxxxxxx"'
- Add "Logger" Component for debugging and Console output.
- Run the Mule App.
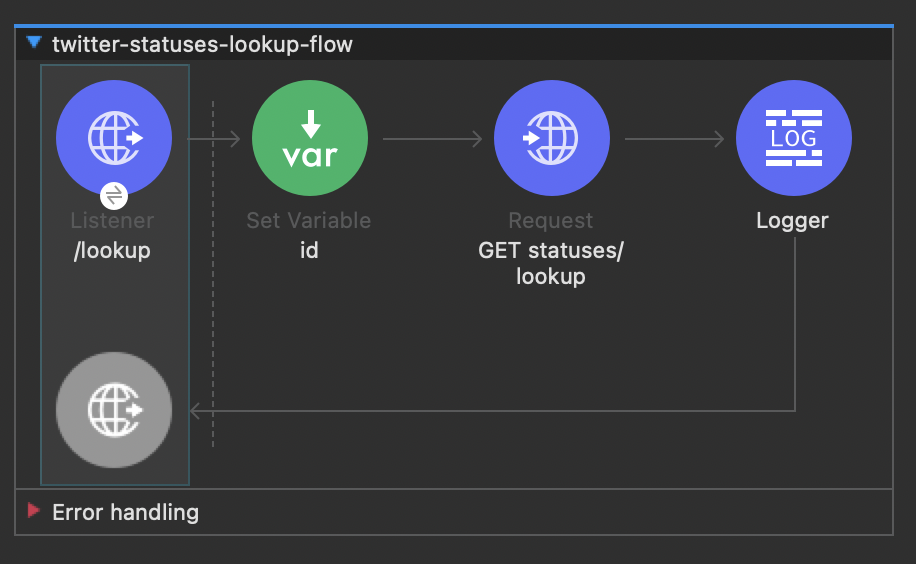
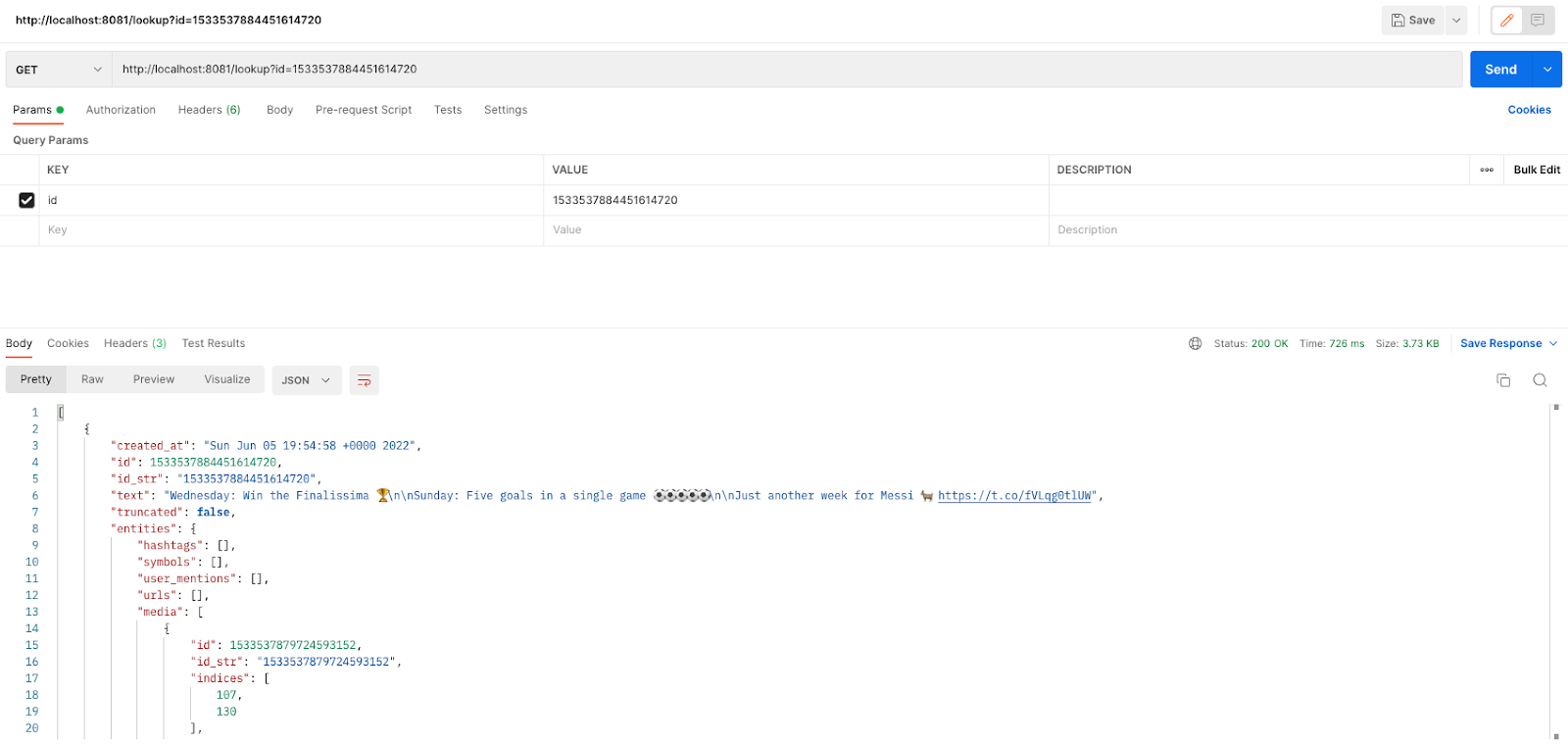
- Test it out using REST Clients - Postman, Advanced Rest Client etc. Following output would be seen.
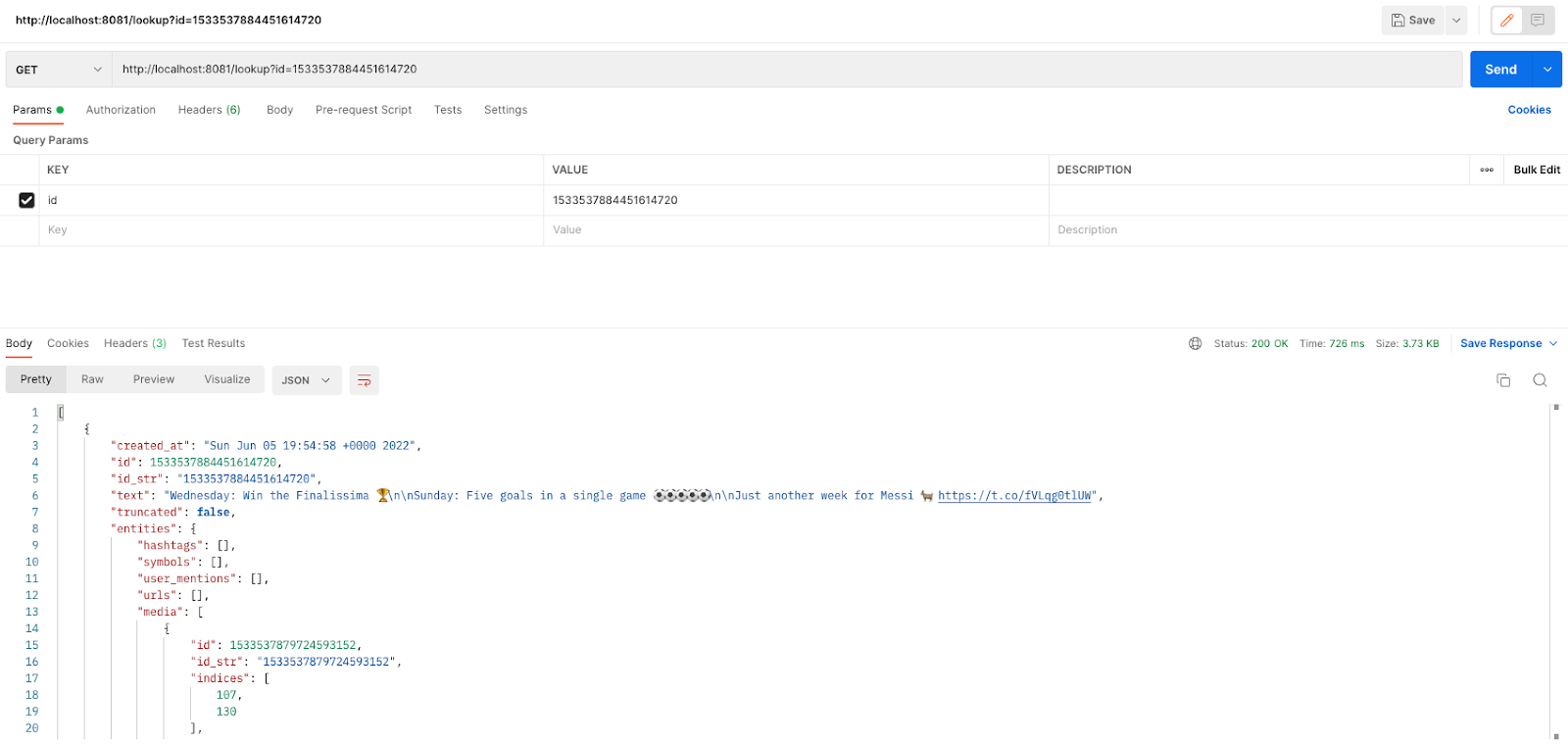
- Test the same URL with the same id value after a day or so. You would see the output as shown in the screenshot below.
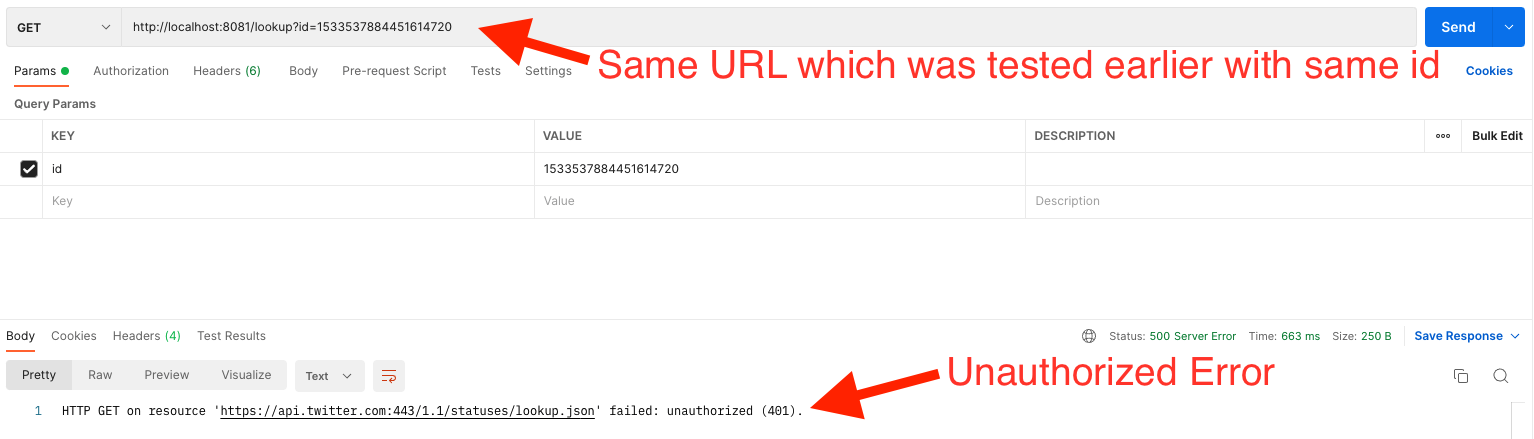
- There are a lot of parameters involved in the flow needed for authentication between the consumer and service provider endpoints.
- And further it gets complicated for certain parameters are time sensitive.
oauth_timestamp="1654799727",oauth_nonce="kYjzVBB8Y0ZFabxSWbWovY3uYSQ2pTgmZeNu2VS4cg"
- We need to dynamically compute oauth parameters' values.
- Create a Mule project and copy the generated values which would be saved in a configuration file under resources.
twitter: host: "api.twitter.com" oauth: consumer_key: "4xxxxxxxxxxxxxxxxxxxxxxxx" consumer_secret: "Txxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx" access_token: "1xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx" token_secret: "Vxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx" signature_method: "HMAC-SHA1" version: "1.0"
- HTTP listener component with default HTTP Connector listener configurations and user defined path.
- Set Variables component taking value from the query params.
- Two Transform Message components to dynamically compute values for required parameters' needed for OAuth 1.0a authentication and values stored in "oauth_signature" and "authorization_header" variables.
First transform component - Dynamically compute values using Mule 4 DataWeave 2.0
%dw 2.0
output application/json
import dw::Crypto
import toBinary from dw::core::Numbers
import withMaxSize from dw::core::Strings
import toBase64 from dw::core::Binaries
import * from dw::core::URL
var http_method = "GET"
var base_url = "https://api.twitter.com/1.1/statuses/lookup.json"
var query_string = attributes.queryString
var oauth_consumer_key = Mule::p('oauth.consumer_key')
var oauth_nonce = toBase64(toBinary(randomInt(99999999999))) withMaxSize 32
var oauth_timestamp = now() as Number
var oauth_signature_method = Mule::p('oauth.signature_method')
var oauth_token = Mule::p('oauth.access_token')
var oauth_version = Mule::p('oauth.version')
var consumer_secret = Mule::p('oauth.consumer_secret')
var oauth_token_secret = Mule::p('oauth.token_secret')
var parameter_string = query_string ++ '&oauth_consumer_key=' ++ oauth_consumer_key ++ '&oauth_nonce=' ++ oauth_nonce ++ '&oauth_signature_method=' ++ oauth_signature_method ++ '&oauth_timestamp=' ++ oauth_timestamp ++ '&oauth_token=' ++ oauth_token ++ '&oauth_version=' ++ oauth_version
var signature_base_string = http_method ++ '&' ++ encodeURIComponent(base_url) ++ '&' ++ encodeURIComponent(parameter_string)
var signing_key = consumer_secret ++ "&" ++ oauth_token_secret
var signature = toBase64(Crypto::HMACBinary(signing_key as Binary, signature_base_string as Binary, "HmacSHA1"))
---
{
http_method: http_method,
base_url: base_url,
query_string: query_string,
oauth_consumer_key: oauth_consumer_key,
oauth_token: oauth_token,
oauth_signature_method: oauth_signature_method,
oauth_timestamp: oauth_timestamp,
oauth_nonce: oauth_nonce,
oauth_version: oauth_version,
consumer_secret: consumer_secret,
oauth_token_secret: oauth_token_secret,
signing_key: signing_key,
parameter_string: parameter_string,
signature_base_string: signature_base_string,
signature: signature,
oauth_signature: encodeURIComponent(signature)
}
Second transform component - Setting the dynamically computed values in "Authorization" variable in HTTP request component.
%dw 2.0 output application/java --- 'OAuth oauth_consumer_key="' ++ vars.oauth_signature.oauth_consumer_key ++ '",oauth_token="' ++ vars.oauth_signature.oauth_token ++ '",oauth_nonce="' ++ vars.oauth_signature.oauth_nonce ++ '",oauth_timestamp="' ++ vars.oauth_signature.oauth_timestamp ++ '",oauth_signature_method="' ++ vars.oauth_signature.oauth_signature_method ++ '",oauth_version="' ++ vars.oauth_signature.oauth_version ++ '",oauth_signature="' ++ vars.oauth_signature.oauth_signature ++ '"'
- HTTP request component with default HTTP Conector request configurations for host as Twitter and user defined path.
- Add "Logger" Component for debugging and Console output.
- Run the Mule app.
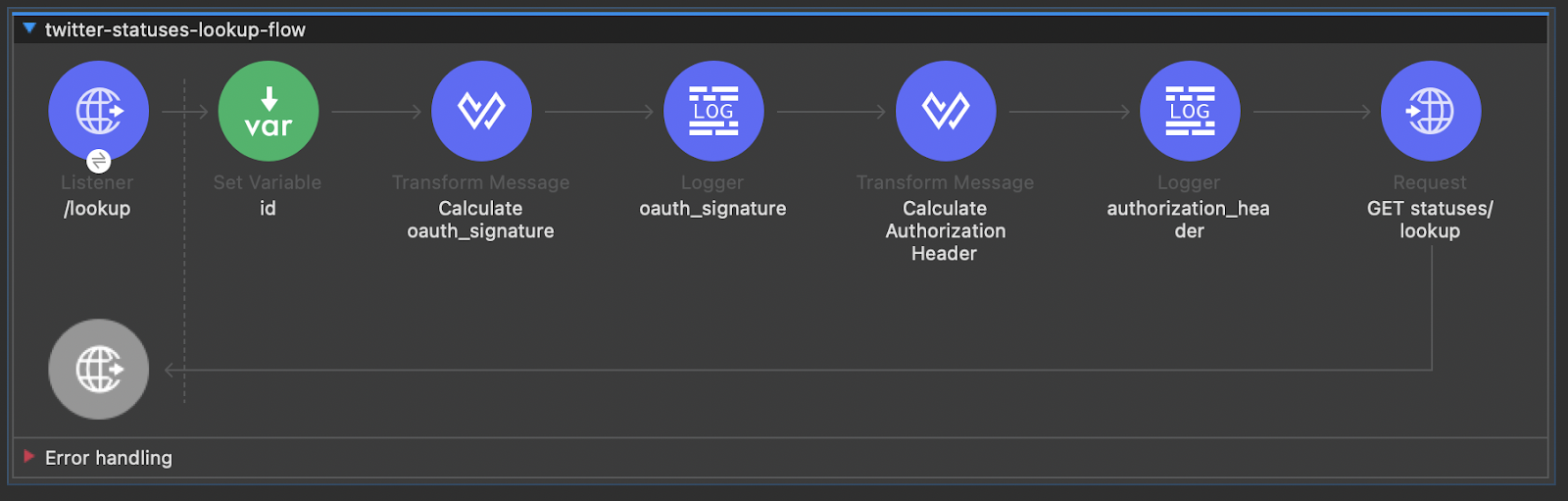
- Test it out using REST Clients - Postman, Advanced Rest Client etc. Following output would be seen.
You can effortlessly use Anypoint Studio (Mule 4) flow along with a few lines of code in DataWeave 2.0, to send OAuth 1.0a authenticated requests to Twitter or to any application requiring OAuth 1.0a.
Happy Learning.